Infrastructure
Infrastructure
IT Infrastructure forms the foundation of modern digital ecosystems, enabling organizations to operate securely, efficiently, and at scale. A well-architected infrastructure ensures seamless connectivity, high availability, and optimized resource utilization. As businesses evolve, key aspects such as DevSecOps solutions, virtual environment management, and cybersecurity play a crucial role in maintaining system integrity and performance. Additionally, practices like performance testing and IT outsourcing help organizations enhance reliability and adapt to changing demands. A robust IT infrastructure is essential for driving innovation and sustaining long-term business growth.
DevSecOps Solutions
DevSecOps solutions are transforming digital infrastructure by integrating security into the software development lifecycle, addressing the increasing costs of cyber breaches, which averaged $4.35 million in 2022. This approach shifts security from a gatekeeping function to a collaborative, proactive role that enhances both security and development efficiency. Key components of modern DevSecOps architecture include continuous security testing, infrastructure as code (IaC) security, and automated compliance monitoring. It also emphasizes security-first design principles, where security decisions are made early in the development process, reducing vulnerabilities.
Selecting the right SMEs involves balancing technical qualifications, industry experience, and cultural fit. A systematic approach ensures that SMEs possess the necessary certifications, hands-on experience, and communication skills to support projects effectively. Additionally, knowledge transfer and proper documentation are crucial to overcoming challenges in outsourcing. A structured knowledge-sharing framework can significantly reduce time wasted on information retrieval and improve project efficiency.
Management of virtual environments
Virtual machines (VMs) are essential in modern enterprise infrastructure, offering flexibility and resource efficiency. However, managing VMs efficiently presents challenges such as performance issues, resource wastage, and security vulnerabilities.
Key components of virtual infrastructure include virtualized compute, storage, and networking, each working together to enhance resource allocation and management. Effective resource optimization involves managing CPU, memory, and storage to ensure peak performance without wasting capacity. Techniques like solid-state drives (SSDs) for critical workloads and dynamic tiering for storage can significantly improve performance. Network performance tuning helps manage data traffic and reduce delays.
Automation tools like orchestration platforms and autoscaling help streamline VM management, reducing manual labor and ensuring operational efficiency. Monitoring tools provide real-time insights into the environment, while automated alerts notify teams of performance changes.
A strong security framework is essential, incorporating access control, network isolation, and compliance management. Security tools like Microsoft Entra ID, Azure Policy, and Defender for Servers help safeguard the infrastructure.
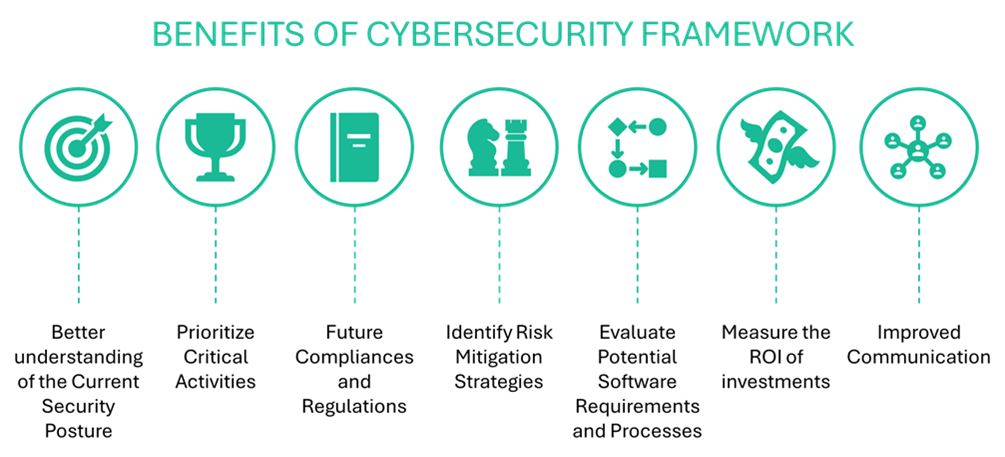
Cybersecurity
Cybersecurity has become a critical business priority as cyber attacks evolve, with organizations losing an average of $4.35 million per breach. This guide explores how organizations can enhance digital infrastructure resilience using established frameworks, such as the NIST cybersecurity framework and zero-trust principles. It covers identifying system vulnerabilities, implementing robust security measures, and ensuring business continuity.
Performance test
Performance testing is crucial for preventing infrastructure issues that can lead to costly downtime, with businesses losing $5,600 every minute during system failures. Modern performance testing tools have advanced significantly, providing comprehensive evaluations for complex digital infrastructures. This article outlines strategies for developing robust performance testing frameworks tailored to cloud-native architectures, containerized environments, and distributed systems.
Key components of performance testing include:
- load testing
- stress testing
- scalability testing
- latency testing
Automation tools streamline the process by integrating testing into Continuous Integration/Continuous Deployment (CI/CD) pipelines, enabling early issue detection and reducing manual efforts. Infrastructure as Code (IaC) testing ensures consistent, reliable deployments, addressing challenges like configuration drift and resource sprawl.
IT outsourcing & SME’s
Subject Matter Experts (SMEs) play a pivotal role in the success of IT outsourcing projects by bridging the gap between internal teams and outsourcing partners. They bring specialized expertise in specific technologies, systems, and processes, ensuring high-quality deliverables, effective communication, and strategic solutions throughout the outsourcing lifecycle. SMEs help define technical solutions, ensure compliance with industry standards, develop training programs, and improve processes, directly influencing project success rates.
To successfully implement DevSecOps, organizations must focus on assessment, technology selection, and change management. By automating security tasks such as vulnerability scanning and penetration testing, DevSecOps reduces human error and accelerates the development cycle. Measuring success involves tracking key performance indicators (KPIs) such as vulnerability tracking, recovery times, and compliance adherence, which help calculate ROI and performance improvements.